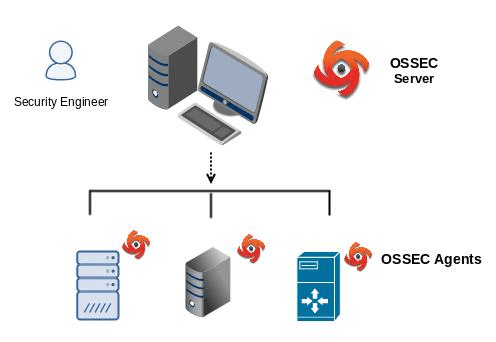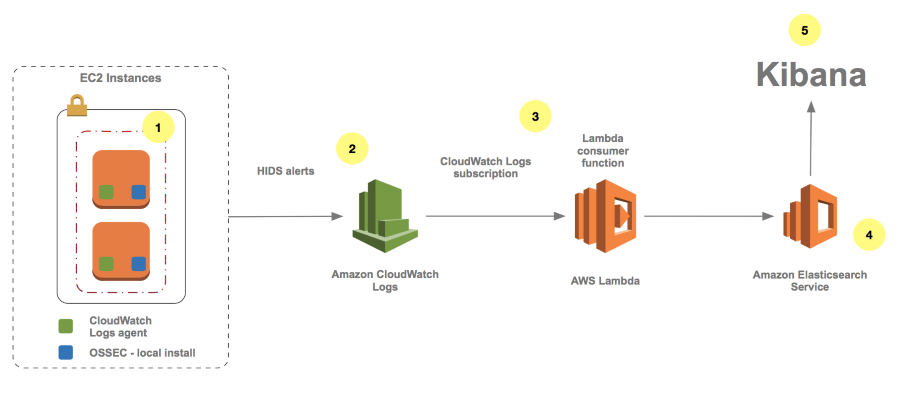
How to Monitor Host-Based Intrusion Detection System Alerts on Amazon EC2 Instances | AWS Security Blog
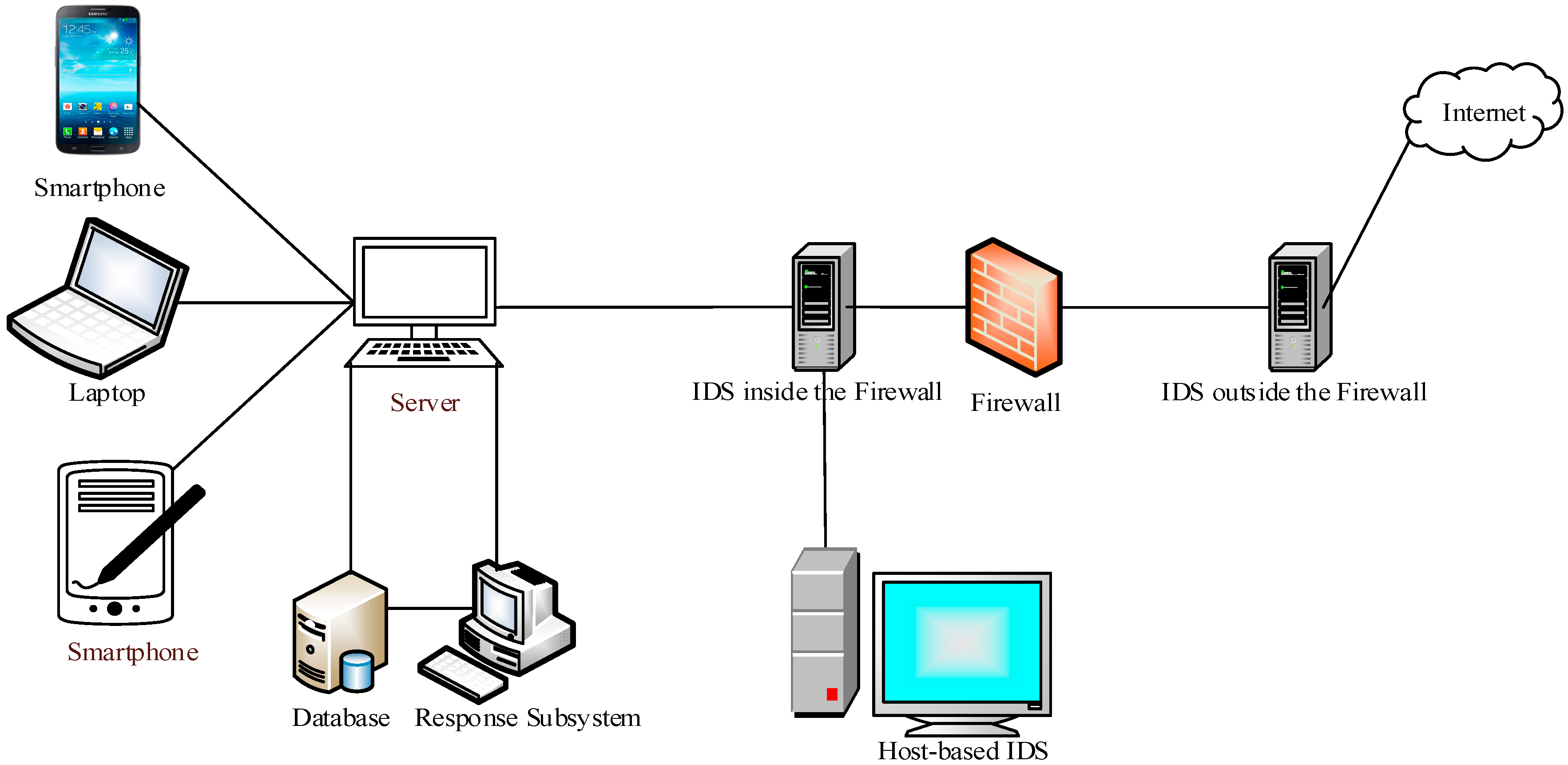
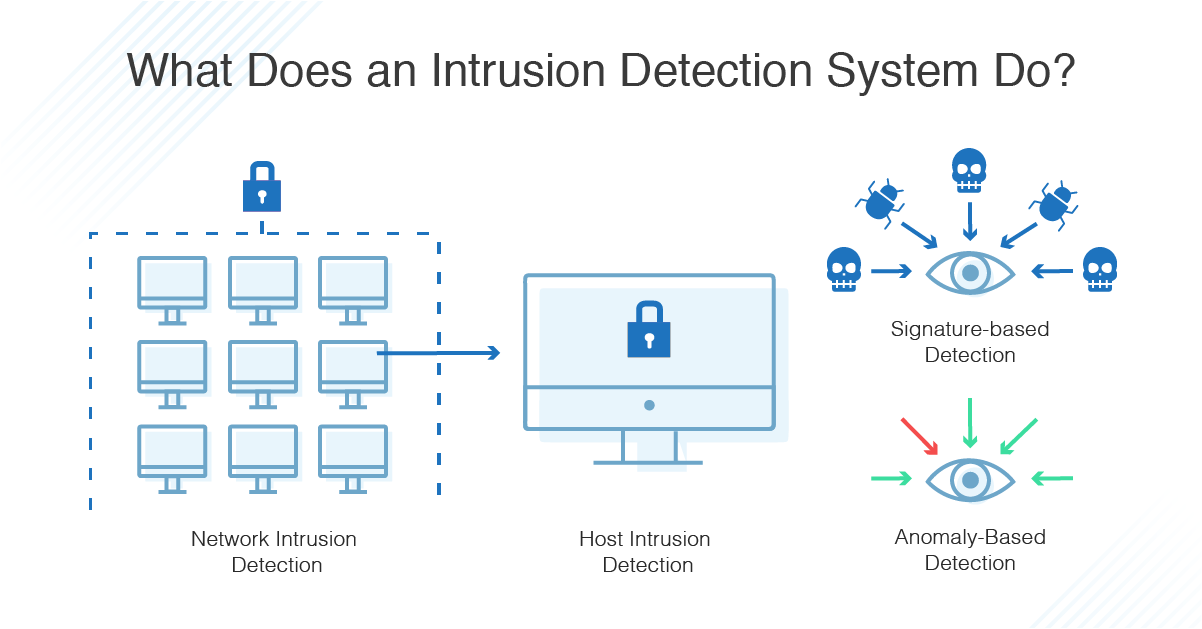
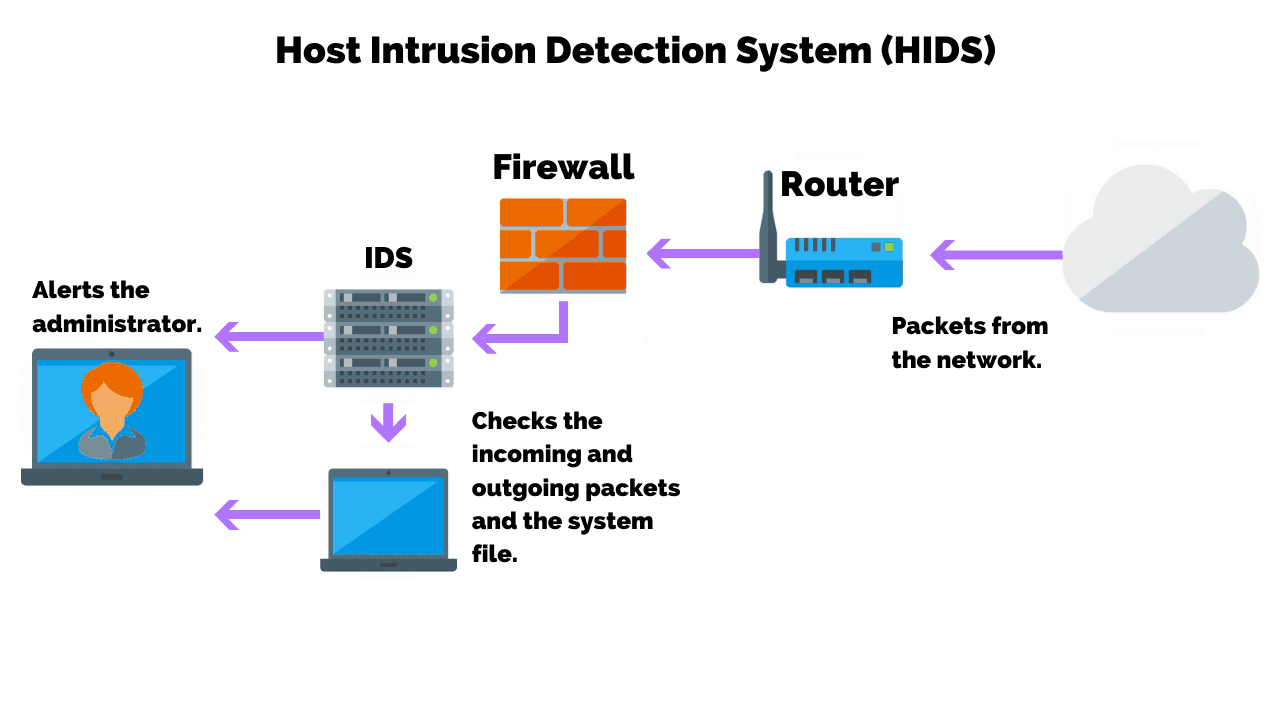
Algorithms | Free Full-Text | From Intrusion Detection to an Intrusion Response System: Fundamentals, Requirements, and Future Directions
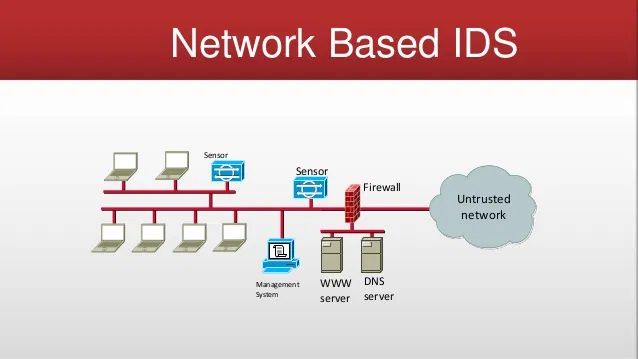
![PDF] Intrusion Detection : Host-Based and Network-Based Intrusion Detection Systems | Semantic Scholar PDF] Intrusion Detection : Host-Based and Network-Based Intrusion Detection Systems | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/471b6047150e82d5b94cbcf1fed36586dcf929c1/6-Figure1-1.png)
PDF] Intrusion Detection : Host-Based and Network-Based Intrusion Detection Systems | Semantic Scholar
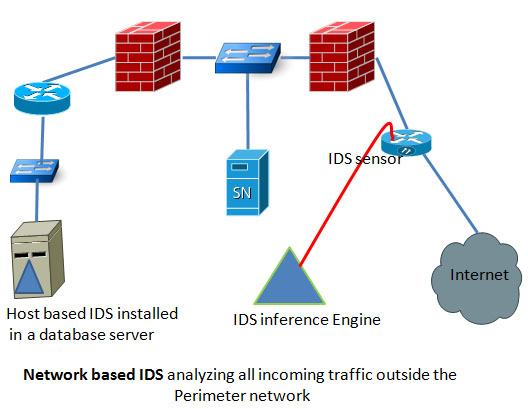
A classical architecture of host and network-based intrusion detection... | Download Scientific Diagram